Author: AMLOfficer Team
Internal Compliance Architecture for Crypto Exchanges: From Auto-Scoring to SAR
A high-quality compliance system is not merely about manually checking passports; it is a complex process consisting of three layers: decision-making procedures, analytical software, and quality data collection (KYC/SOF).
We will break down what the compliance mechanism looks like from the inside, based on modern FATF standards and the real-world practice of AML officers.
1. The Procedural Layer: The Decision-Making Algorithm
The foundation of any Virtual Asset Service Provider (VASP) is a formalized Data Flow. The decision to block or process a transaction cannot depend on a human operator's mood. It must rely on a cascading model of risk decision-making for each individual case. Crucially, this decision-making mechanism remains universal for everyone.
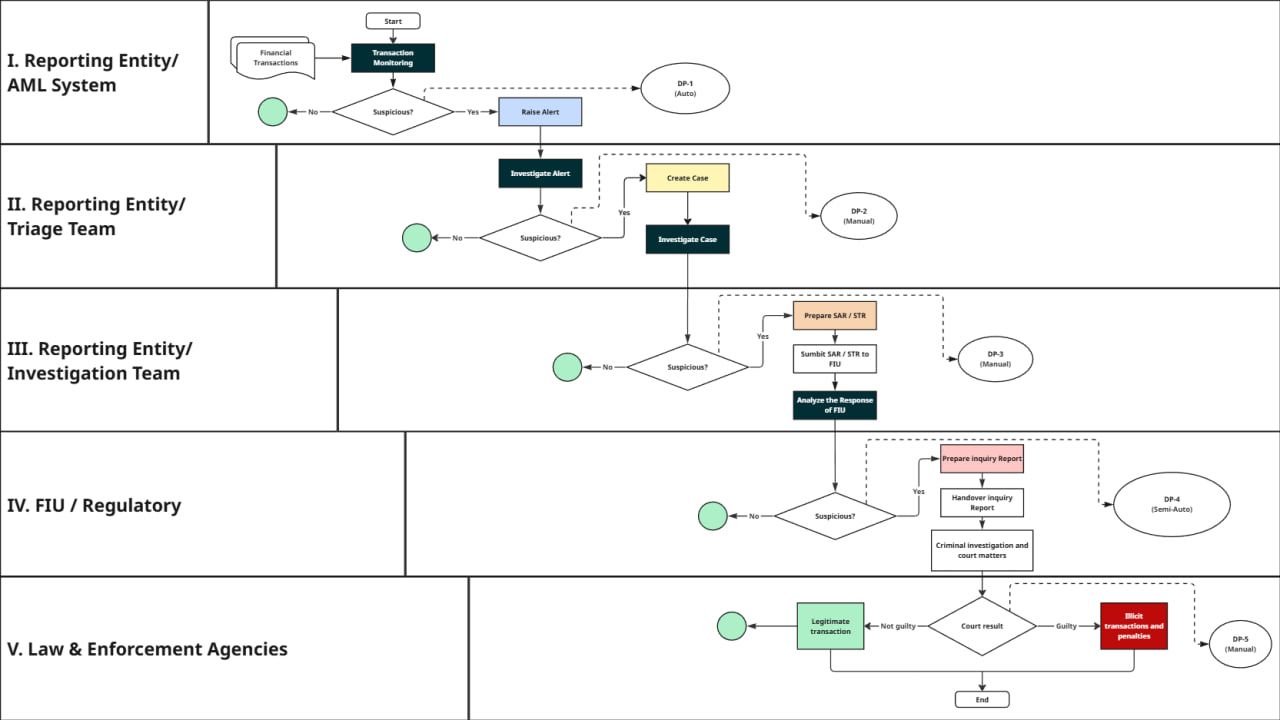
Stage I. Automated Pre-Assessment (DP-1 Auto)
The first stage of risk determination is the AML screening of the transaction. As soon as a transaction hits the service's wallet, it passes through an AML service that verifies the source of funds.
- Goal: Automatic identification and filtration of transactions containing Severe Risk indicators without operator involvement.
- Logic: The AML service scans the transaction for high-risk assets in the sender's wallet (e.g., Sanctions, Terrorist Financing, Ransomware, Darknet, Scam, etc.).
- Result: Either "Automatic Confirmation" or "Red Flag" (Alert).
Stage II. Risk Qualification (DP-2 Manual)
The alert reaches a Level 1 specialist. A manual analysis is performed here to check for false positives .
- Case: A client transferred funds from a mixer, but the amount is insignificant, and the wallet history is clean.
- Decision: The specialist evaluates the company's risk appetite. If the transaction falls into Critical Risk categories (Sanctions, TF, Ransomware, Darknet, Scam, etc.), a full-fledged incident (Case) is created.
Stage III. Deep Investigation (Investigation Team)
The key stage of internal compliance. A Senior Officer steps in here.
- Investigate Case: Deep OSINT is conducted, documents (KYC/SOF) are requested, and a link graph is built.
- DP-3 (Manual): Final internal assessment.
- Decision: If the client cannot explain the origin of funds or the link to Illicit Activity is obvious (Critical Risk), the VASP is obliged to prepare a Suspicious Activity Report (SAR/STR) and submit it to the regulator.
Stage IV. Regulatory Oversight (FIU / Regulatory)
After sending a SAR, the initiative shifts to the Financial Intelligence Unit (FIU).
- Response Analysis: The regulator analyzes the received data.
- DP-4 (Semi-Auto): Assessment of the validity of suspicions at the state level.
- Decision: If the regulator sees the composition of a crime, an investigation report is formed, and the case is transferred to law enforcement.
Stage V. Law Enforcement
The final stage, where the exchange acts as a witness, executor, or data source.
- Criminal investigation and court proceedings.
- DP-5 (Manual): Court result.
- Outcome:
- Not Guilty: The transaction is recognized as legitimate, and funds are unfrozen.
- Guilty: Assets are recognized as illicit; fines or confiscation follow.
Important for VASPs: Note that after Stage III (SAR submission), the VASP loses control over the process. Attempting to return funds to the user at Stages 4 and 5 without sanction from the authorities may qualify as a violation of the law.
2. OSINT as a Necessary Tool for Security
The OSINT (Open Source Intelligence) process within a VASP must be as formalized as KYC and on-chain analysis. This means having a standardized playbook: which sources are checked first, how screenshots and links are recorded, how source reliability is assessed, and how OSINT results integrate into the final case risk scoring.
It is vital that OSINT does not turn into "mood-based Googling" by a specific analyst — conclusions must be reproducible, verifiable, and understandable for an external auditor or FIU.
The combination of On-chain Analytics and OSINT radically strengthens decision quality at DP-3.
- If the AML service shows high risks, but OSINT does not confirm a link to real illegal activity, the case may remain in the "Increased Risk without SAR" zone under enhanced monitoring.
- If OSINT reveals clear signs of a scam project, darknet marketplace, or sanctions evasion (even with a partially "clean" on-chain trace), this is a strong argument for escalation, blocking, and filing a SAR/STR.
3. Red Flags in OSINT for Crypto Investigations
| Red Flag Category | Examples of OSINT Signals | Decision (DP-2 / DP-3) |
|---|---|---|
| Website & Project Domains | Recent domain registration despite claims of "years of history"; frequent domain changes/mirrors; hidden/fake WHOIS (offshore registrars, disposable emails); content/design copied from other services. | DP-2: Escalate to increased risk, request project explanation and basic SOF. DP-3: If combined with on-chain risks — EDD, potential block, SAR prep. |
| Social Media & Team Footprint | No real team (AI-generated photos); biographies not confirmed on LinkedIn/News; mass bot comments; aggressive marketing promising "guaranteed returns." | DP-2: Flag as "Suspicious Project," request docs on role/structure. DP-3: If client manages/sells for such a project + on-chain scam indicators — block risky tranches, SAR. |
| Reputation & User Complaints | Series of complaints on Reddit/forums regarding non-refunds or unjustified blocks; project listed in "Scam" or "Blacklist" sections; disconnect between official status and user experience. | DP-2: Request proof of legitimacy (contracts, invoices), potential temporary hold. DP-3: If scam pattern confirmed + victim funds influx — block, escalate, SAR. |
| Regulatory Context | Investor alerts/warnings from regulators; operating as an "exchange" without a license; lawsuits or bankruptcies involving the same entities/directors. | DP-2: Immediate "High Risk" flag, ban simplified onboarding. DP-3: Direct regulator warning = refusal of service, blocking funds, mandatory SAR. |
| Tech Infrastructure | Domains/IPs linked to phishing/illegal casinos; infrastructure in "suspicious" clusters (bulletproof hosting, frequent server rotation). | DP-2: Increase risk score, apply extra on-chain checks. DP-3: Connection to illegal activity confirmed — EDD, block, SAR. |
| Marketing & Funding | MLM/Referral focus; Ponzi signs (high fixed yield, timers, pressure to buy); roadmaps without specifics (no legal entity, no team). | DP-2: Classify as "High Risk Investment," request SOF/SOW. DP-3: Confirmed Ponzi signs + retail influx — block new deposits, notify Risk Committee, SAR. |
| Digital Signals on User | Email/Phone/IP in leak databases or fraud lists; mismatch between KYC and digital footprint (wrong language/country); "Synthetic Identity" signs (clean history for a "serial entrepreneur"). | DP-2: Increase risk score, video-KYC, limit operations. DP-3: Fraud link or synthetic identity confirmed — refusal of service, SAR. |
⚠️ Note: These OSINT red flags are used exclusively for internal risk assessment and must not be directly disclosed to the client to avoid "tipping off" and violating AML laws.
4. AML Triggers: What Specifically Causes a Block?
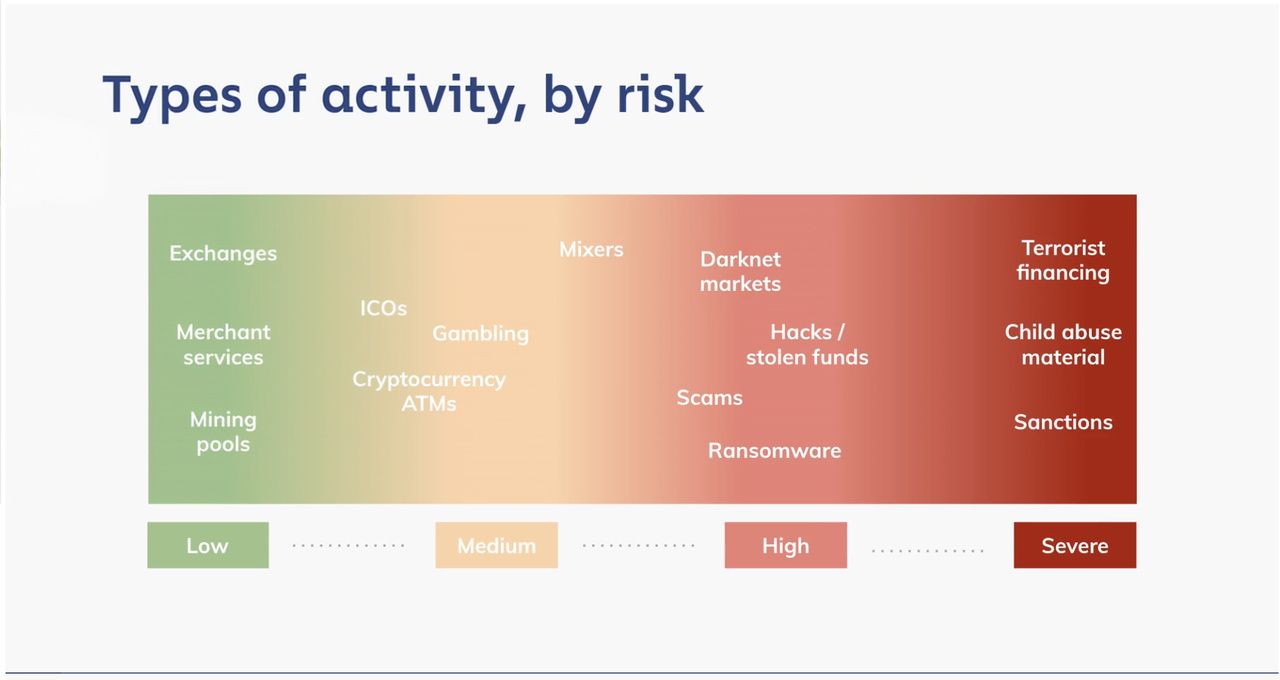
All assets are divided into risk categories. The "cleanliness" of your transaction depends on where the money came from. According to risk classification, blocking is practically inevitable when interacting with High Risk and Severe Risk categories. These include:
- Darknet Market: Direct or indirect connection to dark web marketplaces.
- Fraud Shops & Scams: Funds linked to fake shops or scam projects.
- Mixing Services: Use of mixers to obfuscate trails (a frequent sign of money laundering).
- Ransomware: Funds obtained via extortion/hacking.
- Stolen Funds: Assets tagged as stolen.
- Sanctioned Entities: Addresses on sanctions lists (OFAC, etc.).
If On-chain and OSINT analysis show a link to these categories, the exchange is not "nitpicking"—it is fulfilling a security requirement.
5. The Instrumental Layer: What Do We Analyze With?
Modern crypto compliance is impossible without AML services that analyze transactions. A VASP is obliged to ensure continuous monitoring using automated analysis tools.
An ideal AML service provides:
- Clustering: Understanding that address
bc1q...belongs to a specific exchange or darknet market. - Graph Visualization: Tracking the chain of funds movement (Peeling chains, mixing).
- Risk Scoring: Assigning a numerical risk level to a transaction.
Expert Tip: Regulators recommend subscribing to at least 2 different AML services to have a reliable view of risks. AMLOfficer.org is an aggregator that allows you to check transactions and wallets via four different AML providers simultaneously; therefore, we recommend it for ensuring your transaction security.
6. The Data Layer: KYC/SOF Guide
The hardest question for a VASP: Which documents should we request? Here, the RBA (Risk-Based Approach) applies. Requirements must be adaptive. We have compiled a decision matrix based on jurisdictional risks. Use this table as a cheat sheet for configuring your internal policies.
Document Request Matrix for VASP
| Jurisdiction Type / Risk Level | Examples | Regulatory Status | Permissible Requests | Stop-List (Forbidden Requests) |
|---|---|---|---|---|
| 1. Banned / Sanctioned Zone | China, Afghanistan, Iraq, Bolivia | Crypto is banned de jure or de facto. Legal turnover is impossible. | • Operational Refusal: Full denial of service. • Collection of basic on-chain data solely for sanctions/risk screening. |
• KYC (lack of legal basis). • Client documents (legally pointless and risky). |
| 2. High Risk / "Grey Zone" | Egypt, Morocco, Tunisia | No full licensing, no stable access to banking gateways. | • Explanation of specific transaction purpose. • TXID and wallet addresses. • Limited SOF (Source of Funds) only for the checked operation. |
• Full banking package. • Documents of third parties (relatives, counterparties, etc.). |
| 3. Regulatory Vacuum | St. Vincent, Marshall Islands, Vanuatu | No financial or crypto oversight. Often used by offshore structures. | • Explanation of economic sense of operations. • Proof of wallet control (Satoshi test). • Proof of Address (if available). |
• Tax returns. • Audit reports. • Corporate registries "for show". |
| 4. Partial Regulation | Turkey, India, Russia | Regulator exists, but rules are unstable, fragmented, or changing. | • Standard CDD (Customer Due Diligence). • Source of Funds for specific transaction. • EDD (Enhanced Due Diligence) — only upon risk triggers. |
• Data hoarding ("just in case"). • Non-transactional and irrelevant data. |
| 5. Fully Regulated Markets | USA, EU (MiCA), UAE, Singapore, Canada | Strict licensing regime, mandatory reporting, regulatory control. | • Standard CDD & EDD. • Source of Wealth (SOW) for significant amounts. • UBO Identification. |
• Third-party docs without regulator/court request. • Investigative materials. • Banking secrecy of partners. |
7. KYC as an Indicator for Compliance Decisions
For a crypto exchange and VASP, KYC is not just an "entry filter," but a formalized contour through which almost all compliance decisions pass. The KYC Profile determines the starting risk level, monitoring depth, and the threshold for manual review or SAR escalation. Every DP-step (from auto-scoring to final escalation) relies on the answer: "Who are we serving?"
Risk-Based Approach (RBA) in KYC means the service pre-defines client types, products, and jurisdictions in its policy, and then attaches a mandatory set of KYC controls to each risk profile.
- For clients from fully regulated jurisdictions (US, EU, Singapore), this is standard CDD (ID, sanctions/PEP check, relationship purpose).
- For high-risk clients or complex structures, this is EDD with an expanded package, UBO checks, and enhanced monitoring.
Triggers must be embedded in the procedure matrix: events (volume spikes, new countries, mixer connections, adverse media) that require updating the KYC profile and reviewing limits.
The policy must clearly define where "Simple KYC" ends and "Enhanced Checks" begin.
- Source of Funds (SOF) answers the question: What specific source lies behind the current operation? (salary, asset sale, OTC deal).
- Source of Wealth (SOW) answers: How was the client's total wealth formed?
For mass clients, spot SOF for individual operations is sufficient. A full SOW package is reserved for large turnover, PEPs, offshore structures, and other high-risk profiles. Without satisfactory SOF/SOW for a high-risk client, a case cannot be "closed in green."
8. Document Checklist for KYC in Crypto Services
8.1 Basic KYC (Individuals, CDD)
Mandatory minimum for account opening and low/medium limits.
- Personal Data: Full name, DOB, citizenship, residential address, phone, email.
- ID Document (1 pc): Passport, ID card, or Driver's License (if local law permits).
- Proof of Address (1 pc): Utility bill, bank statement, tax notice, official government letter, or lease agreement (usually < 3 months old).
- Liveness Check: Selfie with ID or biometric check via app.
- Purpose: Brief description (trading, P2P, investment, payments).
8.2 Basic KYC (Corporate, CDD)
For corporate clients and structures.
- Constitutive Docs: Certificate of Incorporation, Articles of Association, Commercial Registry Extract.
- Company Details: Legal name, legal address, registration number, tax ID.
- Structure: Ownership chart, list of directors and signatories.
- UBO Documents: ID and proof of address for every beneficiary ≥ threshold (usually 25%).
- Business Description: Activity type, main counterparties/markets, expected volumes in the service.
8.3 Documents for EDD (Enhanced Due Diligence)
Applied to High Risk, PEPs, complex structures, and anomalous behavior.
- Proof of Income (Individuals): Payslips, employment contract, tax returns, bank statements, asset sale contracts, inheritance, dividends.
- Legitimacy of Business (Corporate): Financial statements (audited if needed), key contracts/invoices, regulatory licenses.
- Risk Questionnaires: PEP declaration, position details, source of capital.
- Media Checks: Enhanced adverse media & sanctions screening results saved in the dossier.
8.4 Documents for Source of Funds (SOF)
Requested for specific flows if volume/frequency exceeds thresholds.
- Bank statement showing the incoming funds.
- Invoices/contracts for the specific deal funding the deposit.
- Asset sale proof (real estate, car, business shares).
- Crypto-source docs: Screenshots/reports from other exchanges, on-chain tracing.
8.5 Documents for Source of Wealth (SOW)
For VIPs, PEPs, and High Risk.
- Consolidated History: CV/Resume of wealth accumulation (business, investment, inheritance).
- Supporting Docs: Business ownership proofs, investment reports, wills/gift deeds, IP license contracts.
8.6 Internal Checklist for the KYC File
- Log of all profile updates.
- Verification dates/methods for ID/Address/UBO.
- Screenshots of Sanctions/PEP checks with timestamps.
- Officer's decision on Risk Level/Limits with date.
- Links to related cases (Alerts, SARs).
9. KYC Risks and Action Algorithms
| KYC Risk Level | Client Profile / Triggers | Min Document Set | Additional Docs (on trigger) | Potential Decision (DP-1 → DP-3) |
|---|---|---|---|---|
| Low Risk | Retail clients from regulated jurisdictions (US, EU, UAE, etc.); transparent income (salary, freelance); small/predictable volumes. | ID (Passport), Sanctions/PEP check, Basic form (purpose), Proof of Address. | Usually none; SOF spot-check only for one-off large ops or limit increase requests. | DP-1: Fast onboarding, standard monitoring. DP-2: False positive checks, brief explanations. DP-3: Rare. SAR only on clear On-chain/OSINT indicators. |
| Medium Risk | Clients from partial regulation/vacuum jurisdictions; freelancers/SMBs with uneven income; growing volumes; multi-service usage. | Basic KYC + Income source description + Expected activity (volumes, frequency, counterparties). | SOF for significant deposits; Business proof (site/contracts); P2P/OTC agreements. | DP-1: Simplified onboarding allowed, but lower alert thresholds. DP-2: Mandatory SOF request on alerts. DP-3: Potential temp block; SAR if SOF unconvincing. |
| High Risk | PEPs; High-risk jurisdictions; Complex corporate structures; Offshore; Large volumes; Active OTC; Mixers/Private pools. | Full KYC (ID, Address, Form, Sanctions); UBO ID & Verify; Detailed Source of Income & Activity. | Expanded SOF (Bank statements, contracts, asset sales); SOW (Wealth history); Corporate reports, Audit. | DP-1: Onboarding only after EDD & Senior Approval. DP-2: Any alert = mandatory SOF/SOW update & freeze. DP-3: Failed EDD/SOW = Block, Refusal, SAR/STR. |
| Extreme Risk / Stop-List | Banned/Sanctioned countries; Terrorist/Ransomware/Darknet links. | Collection of minimal technical data (Address, TXID, IP) for risk screening only. Standard KYC not performed. | Docs requested only via official LEA/Regulator request. Self-collection is legally risky. | DP-1: Refusal of onboarding/service. DP-2/3: Block all attempts; Internal Incident; Mandatory SAR/STR & LEA interaction. |
10. Red Lines: Abusive Information Requests
Remember: A VASP is a private company, not a prosecutor. In compliance practice, there is a concept of "Abusive Information Requests"—demands that violate the Data Minimization Principle.
According to GDPR and FATF guidelines, a Compliance Officer should NOT request:
- Bank statements of third parties (the client's counterparties).
- Full internal accounting/tax returns (unless it is the only way to prove SOW for High Risk).
- Notarized affidavits.
- Audit reports (for standard cases).
Requesting these is legitimate only upon official request from competent authorities (Courts, LEA). Including them in a standard checklist creates legal risks for the exchange.
Summary
Effective compliance is a balance between business security and conversion rates. To achieve this:
- Implement automated monitoring at the entry point.
- Use a Risk Matrix to avoid harassing "clean" clients with excessive checks.
- Minimize risk by using multiple analytical tools. Check out AMLOfficer.org, as we have already implemented such a multi-provider solution for you.
If the situation goes beyond the scope of the article, AMLOfficer experts will provide professional support and recommendations.




